In my previous article , I explain how to setup the Raspberry Pi to be a web server. I also demonstrate searching log files for “footprints” from the IP requests that have been made to your web server. Now, I would like to discuss protecting your web server from becoming a victim to a potentially malicious attack.
Keep your Pi updated!
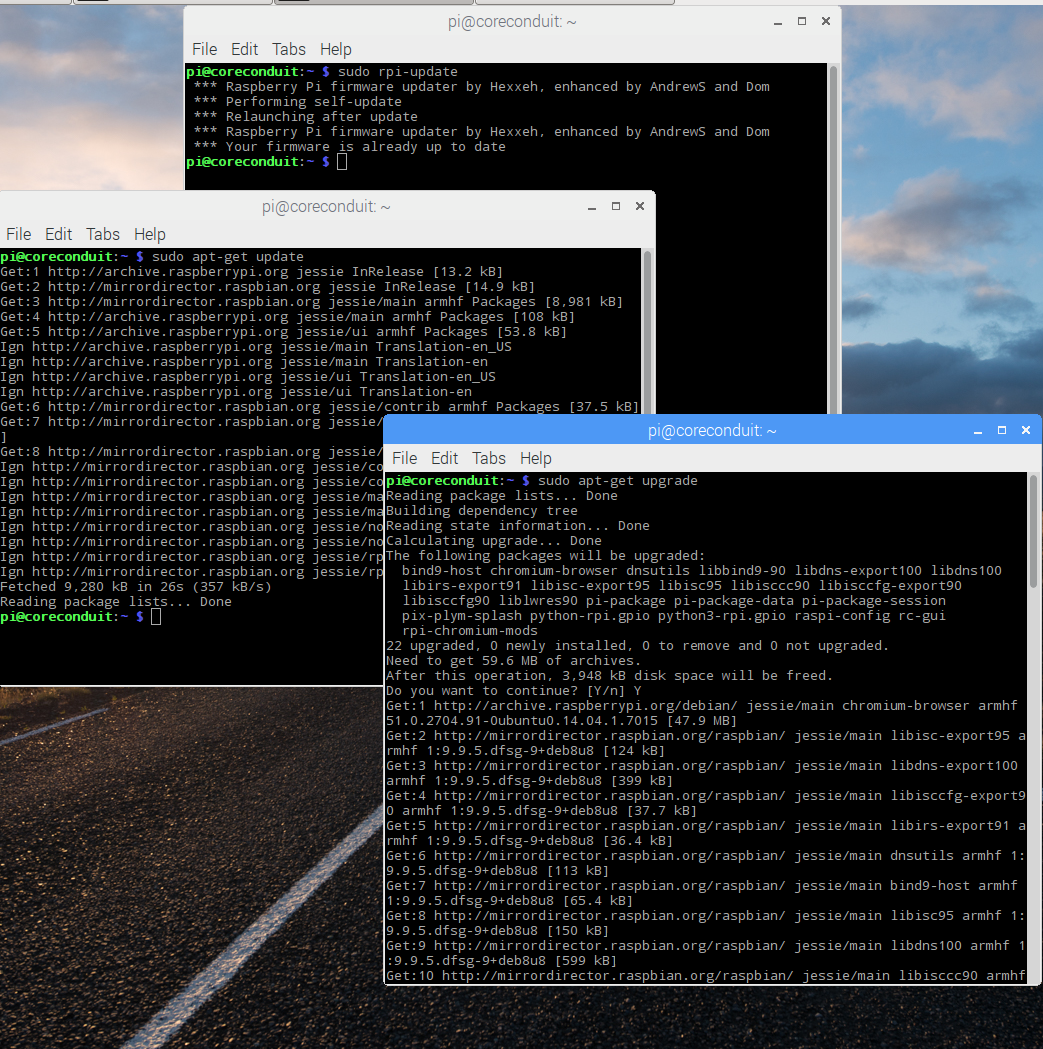
sudo rpi-update
The command will automatically update the Raspberry Pi’s firmware and then ask for a reboot. If your Pi is already up-to-date, then you can continue with:
sudo apt-get update sudo apt-get upgrade
Now, you’ve got the latest and greatest firmware and software!!
Pi Passwords
Ideally, we would disable the default pi account, at the very least, set the default password for your pi account. Another major in-security is that most users have SSH (Secure Socket sHell) and VNC (Virtual Networking Computer) enabled so that they can remote into their machines. I don’t recommend allowing access outside of your network when running a publicly exposed web server.
Apache Web Server
If you are serving web content world-wide then you’ll eventually want to adopt some sort of blacklist, or exclusion list, where you can keep specific IP addresses from accessing your server. However, if you want to tighten-down your security and only allow a select few access then you’ll need to make some changes.
cd /etc/apache2 sudo cp apache2.conf apache2.conf.bak sudo vi apache2.conf OR sudo nano apache2.conf
Travel down the file until you reach this section that allows everyone access to your web server from the outside:
<Directory /var/www/> Options Indexes FollowSymLinks AllowOverride None Require all granted </Directory>
The AllowOverride directive is set to None meaning we will not be using an .htaccess file to override these settings. The next directive, Require is set to all granted, meaning allow anyone access.
UPDATE: I have found a significant number of bot requests in my log files, snooping for those of Us using phpmyadmin, be sure to limit access:
<Directory /usr/share/phpmyadmin/> Order Deny, Allow Deny from All # localhost Allow from 127.0.0.1 # Local-Area Network Allow from 192.168.x.x </Directory>
Next, we can add a directory that we want to protect:
<Directory /var/www/html/hydroMazing/> Options Indexes FollowSymLinks AllowOverride All </Directory>
The AllowOverride directive is set to All meaning we will be using an .htaccess file to override these settings. We will provide the Require directive in our .htaccess file inside the directory we specified, in this case, “/var/www/html/hydroMazing/” One last setting of importance before we save:
# AccessFileName: The name of the file to look for in each directory # for additional configuration directives. See also the AllowOverride # directive. # AccessFileName .htaccess
You could change the name of the .htaccess file here to something harder to guess. Keep the dot at the beginning because it means hidden file. Use your imagination 😉 Now you can use an .htaccess file as your whitelist, or inclusion list:
To create a .htaccess ( or whatever you’ve named it ) file:
cd /var/www/html/mydirectory/ sudo vi .htaccess OR sudo nano .htaccess
# Allow access to localhost Require ip 127.0.0.1 # Allow access to my cell phone Require ip 98.97.34.23
Second entry is an example, change it to your IP address, or the IP address that your web server logged. See my previous article for instructions on checking your log files. Save and close the file. You can add additional access as desired.
Build a Wall
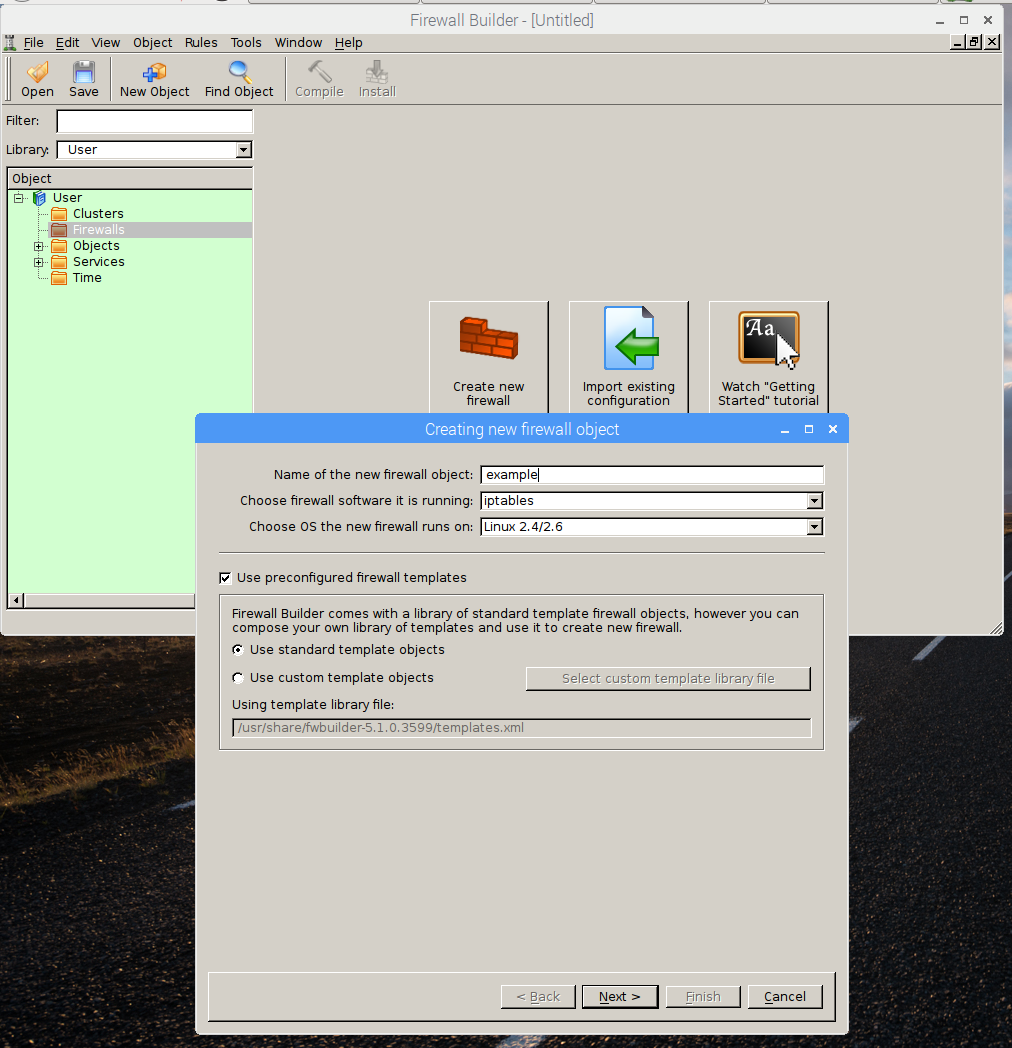
Install the open-source firewall builder
Pop open a terminal from your Raspberry Pi’s desktop and type the following:
sudo apt-get install fwbuilder
After the installation has completed, you will have a new option under the Menu/Internet option from your desktop for the firewall builder GUI.
Add a new firewall and name it the same as your server.
Select the “web server” template to load default rules.
Note that the default rules restrict your server from accessing the outside Internet. In order to allow access, you’ll need to add a rule. The easiest way to add a rule is to copy an existing rule that is similar to your needs.

Compile and Install
We can build our firewall through this interface, but we won’t be able to install it because we won’t have sufficient permissions to write to the file system. Enter the following at a terminal window’s command line assuming you named your server the same as your DDNS name:
sudo mkdir /etc/fw sudo touch /etc/fw/servername.ddns.net.fw sudo chmod 777 /etc/fw/servername.ddns.net.fw
Now, you should be able to use the firewall builder program to compile and install the firewall. You can either restart the apache web server or simply reboot.
Anything incorrect, missing, or not working? Please let me know.